Coordinated Response
Services and tools for incident response management
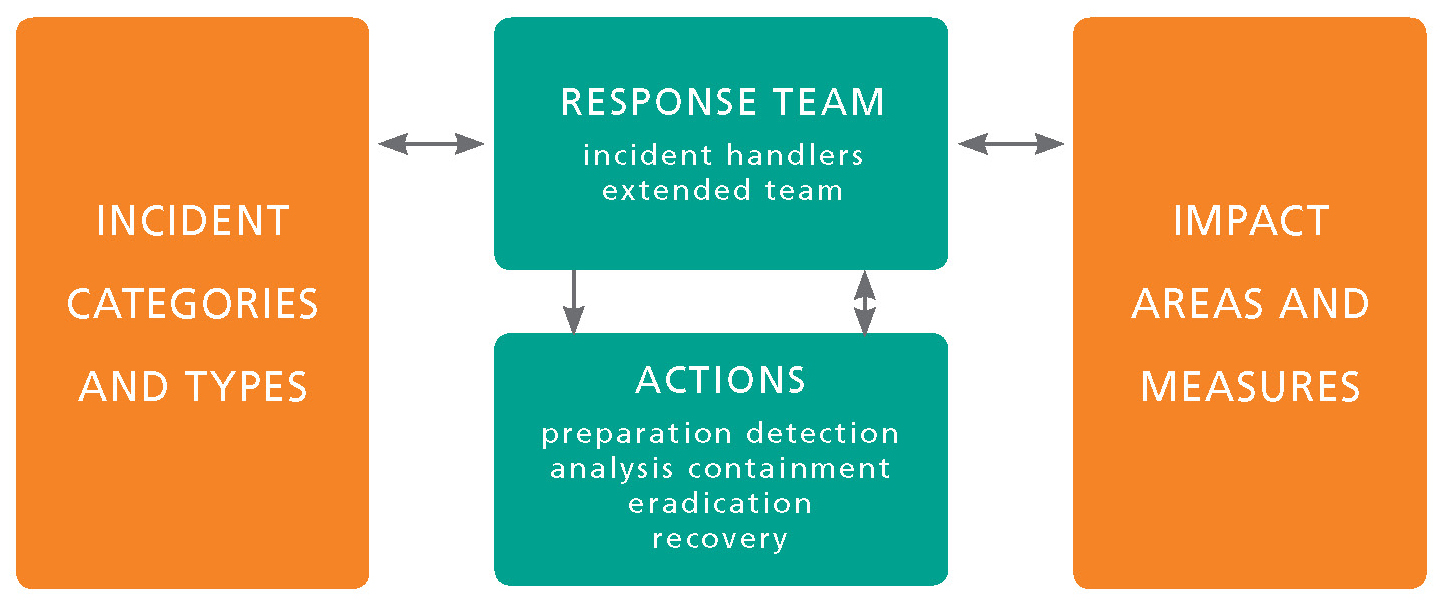
Response Management Framework
Advanced planning leads to a coordinated response for any incident large or small. By eliminating confusion, precious time is saved. But, an effective plan starts with a framework.
A comprehensive incident response plan has multiple dimensions. To avoid missing key elements and costly mistakes, consider response planning from four different angles.
Incident Categories & Types
Events ranging from malware outbreaks to computer equipment loss or theft are addressed in the response plan; define the scope of incident categories to be handled by the response program. Avoid surprises.
Incident Response Team
Departments supporting the core team of responders should be identified and included in the program development as appropriate. Team members need to be aware of their role and responsibilities in advance.
Incident Prioritization / Impact Assessment
Computer security incidents need to be prioritized in a consistent manner. Considering the factors that impact the organization; the higher the impact the higher the priority. Align resources with value.
Incident Response Actions
Response actions should be identified in advance along with the responsible individual or department. Playbooks should be developed to prescribe the sequence of response actions based on the incident type and its potential severity.
Threats, and their potential ramifications, vary greatly, ranging from an easily handled, spyware infected system to a complex and costly (both in dollars and reputation) massive data breach. It is impossible for the incident response team to develop its plan during the crisis. To save valuable time and to avoid costly mistakes the response plan must be created, tested and understood prior to the occurrence of a problem.